Security orchestration automation connects your security tools and automates responses. But who maintains the playbooks? Here's what SOAR vendors don't tell you.

SOAR (Security Orchestration, Automation and Response) platforms integrate security tools and automate incident response. That's the 30-second answer.
Here's what actually happens when you implement one: Your SOC is drowning in alerts. You buy a SOAR platform to orchestrate responses across your security stack—SIEM, EDR, cloud scanner, the works. The demo looked incredible. Your vendor built you three sample playbooks. Six months later, those playbooks are stale, half your integrations broke after vendor API updates, and your one person who understood the logic just left for another job.
This is the dirty secret of security orchestration, automation and response: The platforms work, but someone still has to run them. And that "someone" is usually a security engineer who now splits time between investigating actual security threats and babysitting YAML files.
SOAR stands for Security Orchestration, Automation and Response. It's a category of security platforms designed to integrate multiple security tools, automate repetitive tasks, and standardize incident response workflows.
A SOAR platform typically includes three core capabilities:
Reduce the manual burden on security teams by automating the rote work of triage, enrichment, and initial response. At least, that's the pitch. In practice, it's more like: Trade manual alert triage for manual playbook maintenance. The work doesn't disappear—it just changes shape.
SOAR and SIEM are complementary but distinct:
In a typical architecture, SIEM ingests logs, correlates events, and generates alerts. Those alerts feed into SOAR playbooks, which enrich the data, determine severity, and orchestrate response. Actions and results flow back to SIEM for correlation and documentation.
The confusion arises because modern SIEMs increasingly include response capabilities, and SOAR platforms include detection features. But the core purposes differ—and both require operational capacity to run effectively.
In practice, here's how a SOAR workflow operates:
This process can reduce incident response time from hours to minutes—assuming your playbooks are current, your integrations are working, and someone on your team knows how to modify the logic when business requirements change.
The use cases for security orchestration all make perfect sense on paper. They're the exact workflows that consume the most security analysts' time: Phishing triage, malware response, vulnerability management. Here's what vendors promise versus what you actually get:
The promise: User reports suspicious email → SOAR extracts indicators → checks threat intel → quarantines email across organization → creates ticket if needed.
The reality: Requires integrations with email gateway, threat intel feeds, and ticketing system. Works great until your email provider changes their API, users report emails in formats your parser doesn't handle, or you need to customize logic for VIP accounts. Someone needs to maintain the exception handling.
The promise: EDR detects malware → SOAR isolates endpoint → scans for lateral movement → notifies user → generates incident report.
The reality: Effective isolation requires understanding your network segmentation. Scanning for lateral movement requires up-to-date asset inventory and log correlation. Each step works—until your asset inventory is stale or your EDR upgrade changes how it reports infections.
The promise: Scanner identifies vulnerability → SOAR enriches with exploitability data → prioritizes based on asset criticality → creates tickets for remediation → verifies patch deployment.
The reality: Asset criticality data has to come from somewhere and be kept current. Patch verification requires integration with whatever deployment tool you use. Ticket routing requires knowing org structure and ownership. This use case is incredibly valuable but also incredibly complex to maintain.
Look, I'm not here to trash SOAR. When properly implemented and maintained—and I mean properly, with dedicated resources and continuous refinement—security orchestration automation delivers measurable improvements, including:
I've seen organizations achieve all of these benefits. They're real, not theoretical. But here's what they had in common: Dedicated security engineers who continuously refined playbooks, executive buy-in for ongoing investment, and realistic expectations about what automation can and can't do.
The question you need to answer honestly: Can your team actually achieve and sustain that level of maturity? Or are you one security engineer away from the whole thing falling apart?
The SOAR market has a dirty little secret: Most platforms end up as expensive shelfware because organizations don't account for the operational burden of running them.
Playbooks aren't static. Your environment changes—new tools get added, APIs get updated, business processes evolve, and threat tactics shift. Each change requires someone to modify the playbook logic, test it, and verify it doesn't break existing workflows.
In practice, this means your security engineer who built the original phishing playbook leaves the company. Their replacement inherits 40+ playbooks with no documentation on why specific logic branches exist. A vendor API change breaks three integrations, and no one notices until a critical alert gets dropped.
The uncomfortable question: If your team barely has time to investigate incidents, when are they supposed to maintain the automation that's supposed to save them time?
SOAR platforms advertise "350+ integrations" as a feature. What they don't tell you: each integration is a dependency that can break. APIs change. Vendors deprecate endpoints. Authentication methods evolve. Each integration requires ongoing maintenance—testing, updating, occasionally rebuilding from scratch when vendors make breaking changes.
Before evaluating any SOAR platform, ask: "Who on our team will own integration maintenance?" If the answer is "our one security engineer who's also doing everything else," you're setting up for failure
Effective security orchestration depends on institutional knowledge: why certain alerts get auto-closed, why specific playbooks prioritize certain asset types, why the enrichment logic checks these threat intel sources but not those.
This context usually lives in one person's head. When they leave, you're left with a black box of automation that works until it doesn't—and no one knows why or how to fix it.
Most SOAR implementations follow a predictable arc: initial deployment with vendor-provided playbooks, a customization burst as the team adapts them, a plateau once the "easy" automations are done, then stagnation as ongoing maintenance consumes the time that would go into building new playbooks.
You end up with a partial implementation that automates the simple stuff but still requires manual intervention for anything complex—which defeats much of the value proposition.
If you're evaluating SOAR platforms, don't get hypnotized by the integration count or the slick demo. I've watched too many organizations buy on features and regret it six months later. Ask the harder questions that vendors don't want to answer:
I've seen implementations fail not because the technology didn't work, but because nobody asked these questions during evaluation. The organization assumed "security orchestration" meant "less work for our team" when it actually meant "different work that still requires dedicated headcount." These questions determine whether you'll actually realize SOAR's value or end up with another $200k/year platform that three people log into.
There's an emerging category that addresses SOAR's operational burden: managed security operations platforms. At Mycroft, we built our Risk Operations Center specifically because we kept seeing the same pattern—organizations that needed the capabilities of SOAR but didn't have the operational capacity to run it.
Rather than giving you a SOAR tool and expecting you to run it, platforms like Mycroft's combine automation technology with human operational support. The playbooks exist, the integrations are maintained, and when context transfer is needed, it's handled by the platform team—not your overstretched security engineer.
Here's what traditional SOAR platforms miss: Incident response doesn't happen in a vacuum. Every alert, every vulnerability, every anomaly exists within a broader context of policies, controls, risk tolerances, and compliance requirements.
When you respond to a potential breach, you're not just asking "is this malicious?" You're asking:
Traditional SOAR handles the immediate response—isolate the endpoint, block the IP, create the ticket. But it doesn't connect that incident back to your GRC program, your audit trail, your risk register, or your control framework.
This is the context problem that gets lost in the SOAR conversation. Security operations teams end up with:
When these systems don't talk to each other, critical insights get lost. You might remediate the immediate threat but miss the systemic issue. You might pass your audit but not actually improve your security posture. You might close 100 incidents without understanding the root causes that keep generating them.
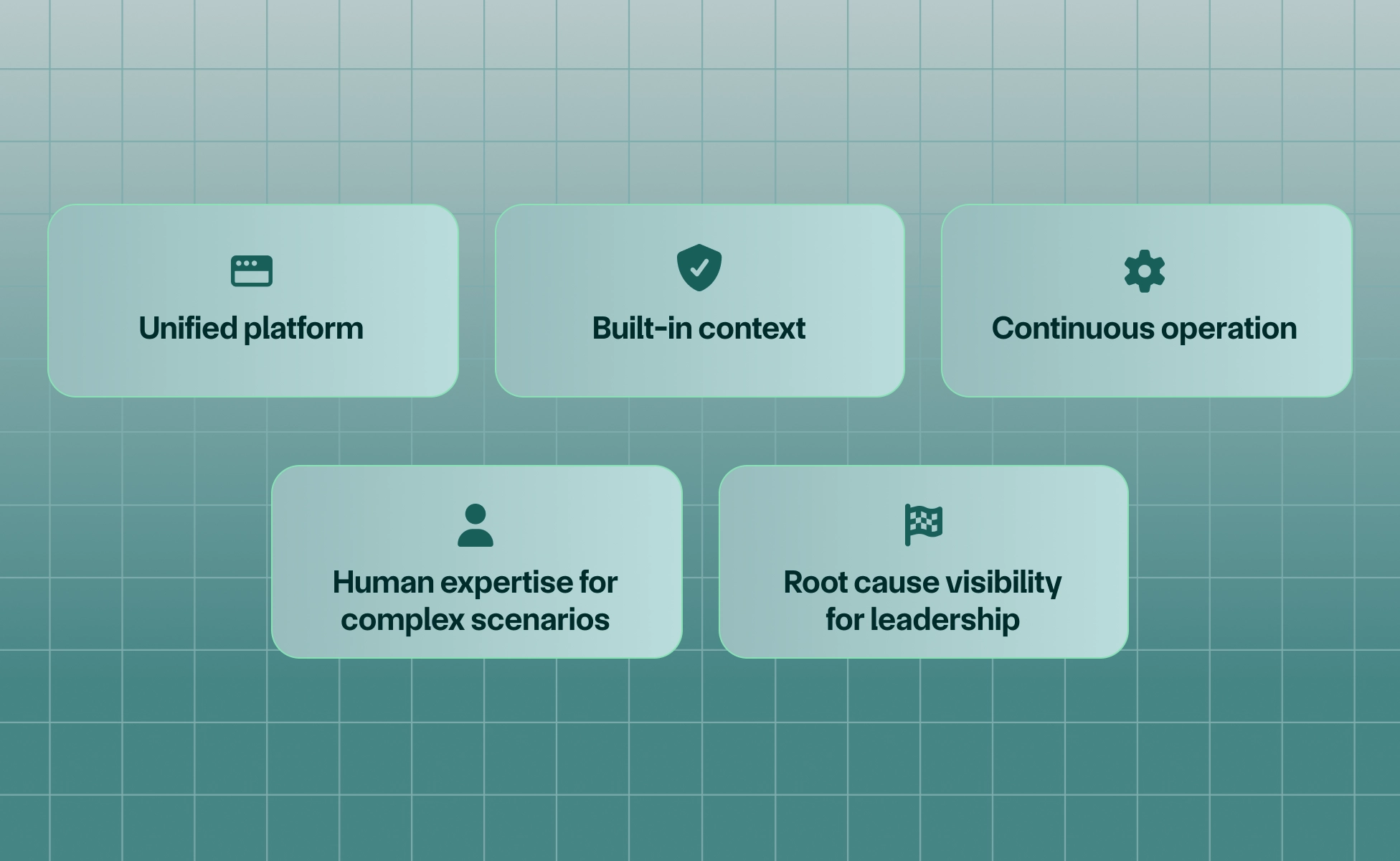
A mature managed security operations platform unifies incident response with the broader security program:
This model makes sense for organizations that:
What this looks like in practice:
The key difference: You're not buying another tool to operate. You're buying operational capacity that connects incident response to your broader security program.
Security orchestration automation works. The technology is sound, the use cases are real, and organizations with mature implementations see measurable improvements in response time and consistency.
But the industry conversation focuses too much on what SOAR can do and not enough on who will make it do it—and keep it doing it as your environment evolves.
Before adopting any SOAR platform, honestly assess whether you have the operational capacity not just to implement it, but to sustain it. And ask whether isolated incident response automation actually solves your problem, or whether you need operational security integrated with your broader GRC program.
The question isn't whether you need security orchestration. The question is whether you need a tool that you run yourself or operational capacity that runs on your behalf—with the context to connect incidents back to policies, controls, and risk.
If you're evaluating how to reduce operational burden without just adding another tool to your stack, exploring a managed security operations model like Mycroft's Risk Operations Center is worth the conversation.
SOAR stands for Security Orchestration, Automation and Response. It refers to platforms that integrate security tools, automate repetitive tasks, and provide structured incident response workflows.
Phishing response (extracting indicators, checking threat intel, quarantining emails), malware containment (isolating endpoints, checking for spread), and vulnerability management (prioritizing patches, creating remediation tickets) are the most common use cases.
Automation executes specific tasks (block an IP, quarantine an email, create a ticket). Orchestration coordinates multiple automated tasks across different tools into cohesive workflows. SOAR platforms combine both.
Traditional SOAR gives you a platform to build and maintain your own automation. Managed security operations combines the platform with operational support—someone else maintains the playbooks, manages integrations, and handles day-to-day operations while you retain decision-making authority. More importantly, managed security operations integrates incident response with your broader GRC program, connecting alerts back to policies, controls, and risk frameworks.
Mycroft provides end-to-end security management (compliance, cloud security, device management, TPRM) with built-in automation and human operational support. Rather than giving you a SOAR tool to run yourself, Mycroft handles operations while you focus on strategic security decisions. Every incident is enriched with context from your compliance posture, control framework, and risk profile—so you see not just "what happened" but "what this reveals about our security program." You get the benefits of orchestration without the burden of maintaining it, and your leadership gets visibility into root causes and trends, not just incident counts.