Build a 2026 risk operations center for SOC 2 security monitoring. Integrate risk & compliance software to cut tool sprawl and boost ERM.
Traditional GRC (governance, risk, and compliance) platforms collect evidence but leave your actual risk exposure unchanged. You're paying for documentation, not protection. These systems archive screenshots and organize policies but cannot prevent misconfigurations or detect unauthorized access. Your cloud infrastructure evolves dozens of times daily through CI/CD (continuous integration/continuous deployment) pipelines and infrastructure-as-code deployments.
Static policies sit in PDF files while your production environment changes continuously. You approve pull requests modifying IAM (identity and access management) roles, deploy containers with updated secrets, and provision cloud resources. Your GRC platform captures none of this activity. It displays last month's control status while your security posture has shifted significantly.
System and Organization Controls 2 (SOC 2) CC7.1 specifically requires continuous operational security monitoring. Auditors expect you to detect security issues promptly and respond systematically. Point-in-time assessments miss security drift happening between review windows. You pass your audit in January, but by March, configuration changes have introduced vulnerabilities.
Modern compliance demands platforms that execute controls, not just archive evidence. You need systems that enforce least-privilege access, detect policy violations in real-time, and remediate misconfigurations automatically.
Tool sprawl creates visibility gaps that turn audit season into crisis mode. You're managing separate vendors for vulnerability scanning, MDM (mobile device management), cloud security posture management, and compliance documentation. Each platform operates independently with its own dashboard, alert system, and data model. None of these tools communicate with each other.
The cost of fragmentation:
The operational burden:
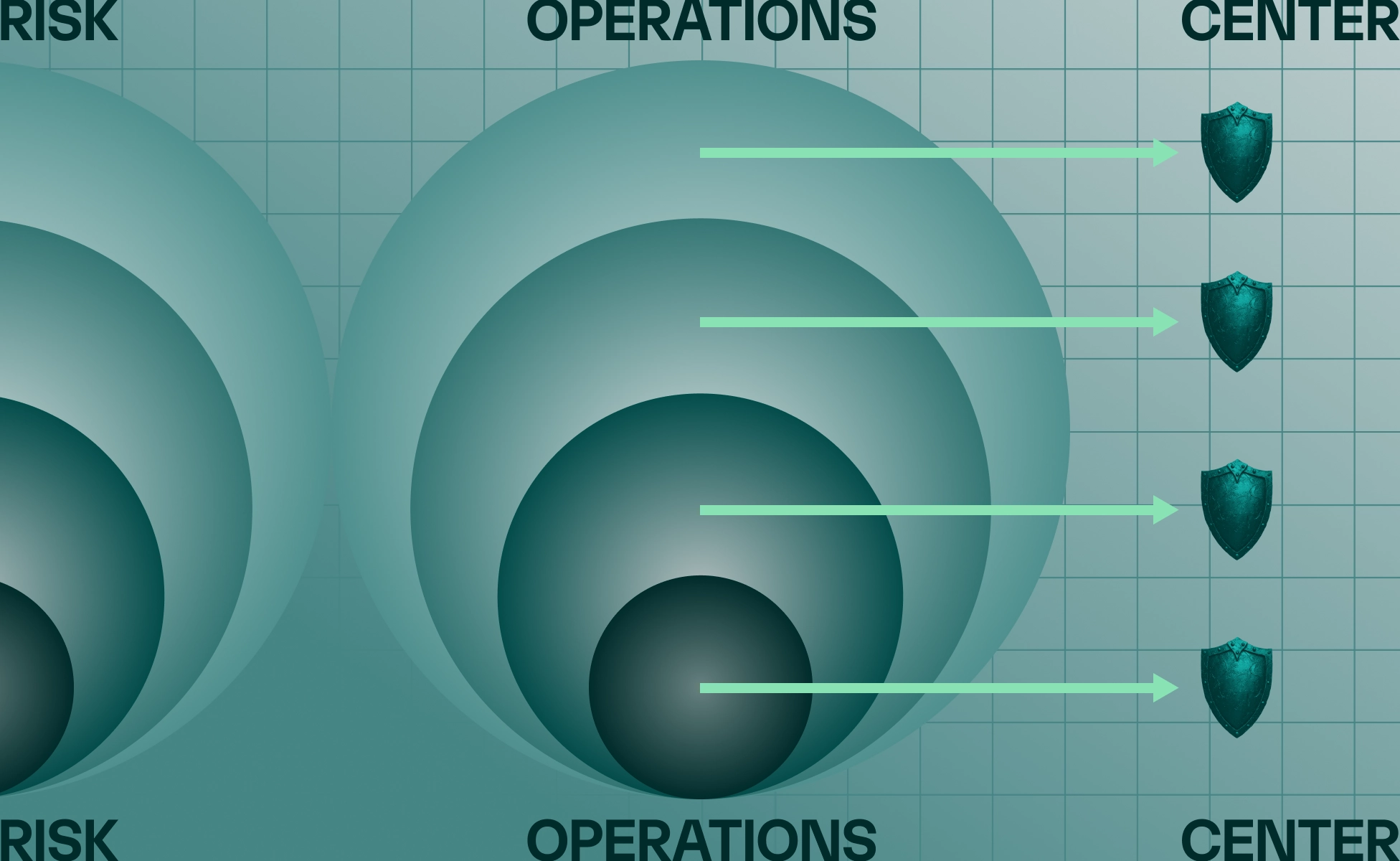
An effective enterprise risk management (ERM) framework connects governance, risk assessment, and compliance through three architectural pillars: dynamic governance, active risk assessment, and automated compliance. These pillars work together in a single automated system that mirrors your actual infrastructure changes in real time.
Dynamic governance:
Active risk assessment:
Automated compliance:
SOC 2 application security monitoring integrates vulnerability scanning directly into your CI/CD pipelines and executes automatically after infrastructure changes. The CC7.1 control mandates this systematic approach to detecting, preventing, and responding to vulnerabilities rather than relying on periodic penetration tests.
Step 1: Continuous automated scanning (Security Lead, DevOps)
Step 2: AI-driven triage and routing (Security Operations, Engineering)
Step 3: Closed-loop evidence tracking (Compliance Manager, Auditor Interface)
Observation period requirements:
A Risk Operations Center (ROC) executes security controls autonomously through AI-driven automation that handles device policy enforcement, access reviews, and vendor risk assessments. This operational model reduces your team's manual workload while improving security posture through faster detection and response cycles.
ROC operational model:
AI-driven automation workflows:
Integrated data model advantages:
Measurable operational outcomes:
Consolidating onto a unified platform reduces vendor sprawl by 40-50% while improving security posture through better data correlation. You eliminate the administrative overhead of managing separate GRC tools, cloud scanners, and MDM solutions that don't communicate with each other.
Cost comparison:
Operational efficiency gains:
ROI (return on investment) drivers:
Strategic advantages:
Q: Is there a difference between a legacy GRC platform and integrated risk and compliance software?
A: Yes. Traditional GRC platforms focus on documentation and evidence storage for annual audits. Integrated risk and compliance software actively implements security controls using AI agents and automation. You get real-time monitoring, automated remediation workflows, and continuous compliance—not just a repository for audit artifacts. The integrated approach reduces vendor sprawl by consolidating GRC, cloud security, and device management into a single platform.
Q: How do you select application security monitoring tools for SOC 2?
A: Start with SOC 2 CC7.1 requirements: vulnerability scanning after significant changes and continuous monitoring capabilities. Your tool must integrate with CI/CD pipelines for automated scanning. Look for API-driven evidence collection that auditors can access without manual screenshot gathering. The platform should map findings to multiple compliance frameworks simultaneously. Verify that the vendor provides audit support documentation but clarifies they don't replace your independent assessment firm.
Q: When should you transition from point solutions to a unified platform?
A: Consider consolidation when you're managing three or more security vendors or spending 20+ hours per month on manual evidence coordination. If audit preparation requires a dedicated sprint each quarter that pulls engineers off product work, you need continuous monitoring capabilities. Calculate your current tool sprawl costs by adding GRC platform fees, cloud scanner licensing, MDM subscription, and consulting support hours. Most startups hit the consolidation inflection point around 50-100 employees.
Q: What implementation timeline should you expect for a risk operations center?
A: Initial platform deployment takes 2-4 weeks for SSO configuration, cloud integration via API keys, and device enrollment through MDM agents. Control implementation happens in waves: critical findings first within days, then medium-priority configurations over weeks, then policy enforcement and automated remediation. Expect 6-8 weeks to achieve continuous monitoring baseline where all core controls operate automatically. Remember: SOC 2 Type II requires a three-month observation period demonstrating sustained control operation, so your total timeline is 4-6 months.
Schedule a risk operations demo to see how Mycroft's unified platform consolidates GRC, application security, and cloud monitoring. Reduce vendor sprawl while maintaining continuous audit readiness. Strengthen your risk operations by cutting your compliance timeline in half.