Move to continuous security monitoring for enterprise readiness in 2026. Automate evidence collection & combat modern threats effectively.
Static audits fail because they become outdated immediately after the auditor signs the final report. System and Organization Controls 2 (SOC 2) creates a snapshot that ignores dynamic modern threats. Relying on annual checks creates gaps because threat actors evolve their tactics every single hour. You need a system that adapts to change rather than one that simply records history.
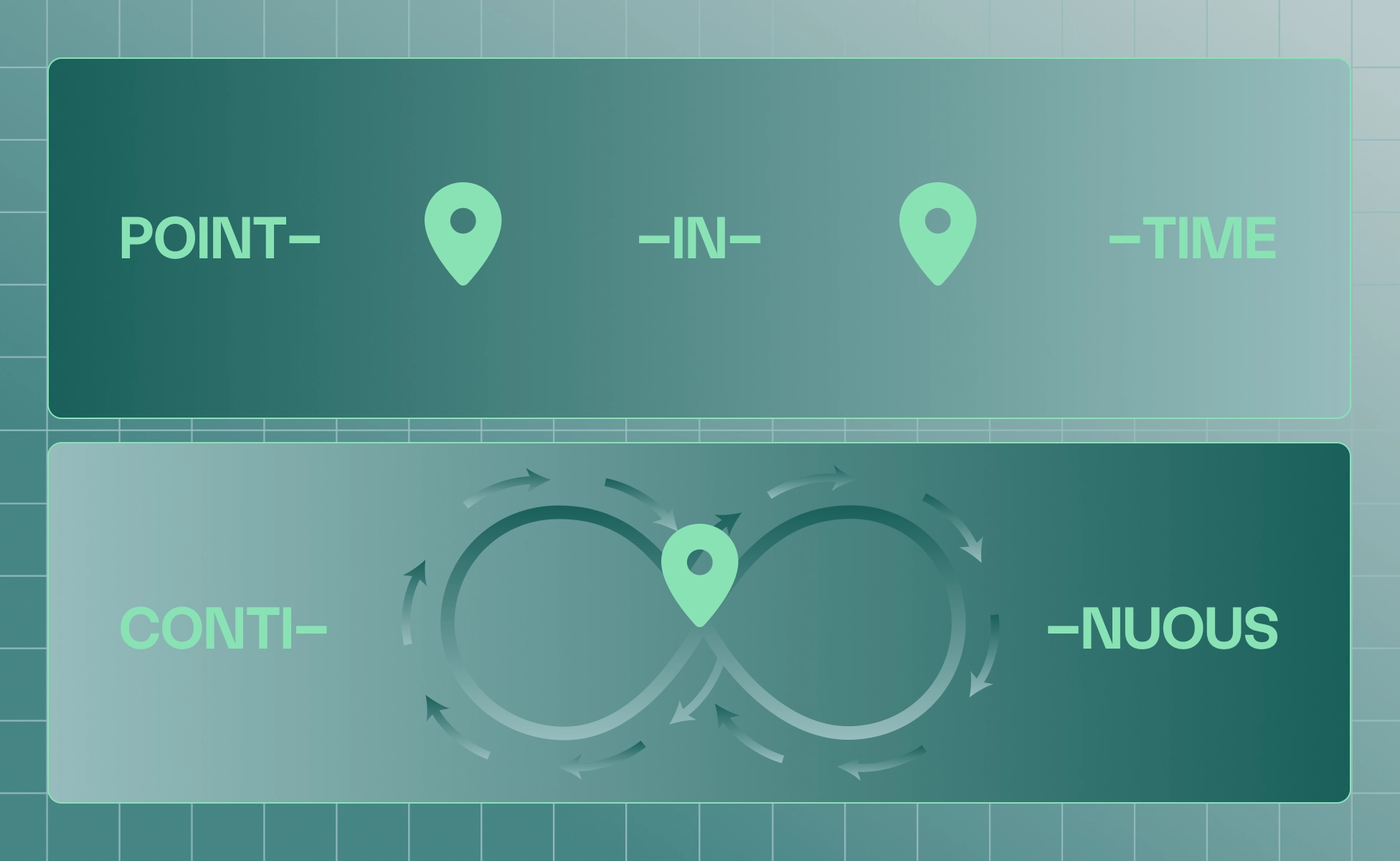
You are relying on obsolete "point-in-time" assessments
Preparing for an annual audit can feel like a high-stakes fire drill for your entire team. You spend weeks fixing findings, but this snapshot remains insufficient against rapidly evolving external threats. Attackers scan for new vulnerabilities minutes after public disclosure , rendering old reports useless. Your annual report cannot protect your infrastructure from a zero-day exploit released this morning.
You are accumulating "security debt" with static reporting
Relying on static PDFs creates a dangerous backlog of unverified controls across your expanding infrastructure. Engineering teams push code daily, yet your compliance evidence sits frozen in a past state. This discrepancy explains why enterprises suffer breaches despite holding valid and clean audit reports. The divergence between paper compliance and actual security posture is security debt that accrues interest.
You need continuous security monitoring to combat rising threats
Continuous validation is the primary method to close the gap between audits and attack surfaces. Exploitation of vulnerabilities has tripled year-over-year according to Verizon’s 2025 Data Breach Investigations Report . Attackers use automated tools to scan perimeters constantly, so manual defense strategies often fail. Continuous security monitoring ensures your defensive posture matches the incredible speed of the current threat landscape.
Automated evidence collection transforms compliance from a manual sprint into a reliable, silent background process. You integrate directly with infrastructure via Application Programming Interface (API) to prove compliance without disruption. This approach respects your engineering team's time while generating proof automatically as they build products.
Stop the engineering drain of manual collection
You likely waste expensive engineering hours on administrative trivia like taking screenshots or downloading logs. This manual process pulls your best talent away from product development and creates internal friction. Automation handles compliance data in the background so engineers focus on high-value architectural work. Your developers should be building features rather than gathering evidence for an annual compliance audit.
Connect your infrastructure for automated SOC 2 tracking
Connecting cloud environments to a compliance platform eliminates the need for manual sampling or checking. The system verifies controls are active and logs evidence to create an immutable compliance record. You no longer need to hunt for proof of encryption or backup execution during audits. The platform queries actual configurations, ensuring that the evidence you present is based on reality.
Shift to "always-on" validation
Automated systems alert you the moment drift occurs rather than waiting for an external auditor. You receive notifications if a firewall rule changes or Multi-Factor Authentication (MFA) is disabled. This allows you to fix issues immediately before they become significant compliance violations. Proactive remediation prevents the frantic "fire drill" that typically happens two weeks before an audit.
Realize immediate Return on Investment (ROI)
Organizations that switch to automated collection see drastic reductions in their administrative and operational overhead. Wisedocs achieved approximately 100% ROI by effectively doubling the value of their security spending. Savings come from reduced billable auditor hours and reclaimed internal time for your engineering teams. Automation turns compliance from a cost center into a streamlined operational process for your business.
The "ready" signal is a live view of security posture that demonstrates active control to buyers. Enterprise trust is won by showing transparency through a Risk Operations Center rather than certificates. Sophisticated buyers prioritize vendors who demonstrate operational maturity through real-time data instead of static documents.
Move from static reports to live signals
A static PDF tells a buyer you were secure months ago during a specific window. A real-time dashboard brings transparency to compliance requirements and proves you are watching the store. Sharing a live view of passing controls differentiates you from competitors hiding behind old PDFs. You build confidence faster when you can prove you are securing the environment right now.
Consolidate visibility in an Active Command Center
You need a single pane of glass where Mycroft’s AI Agents continuously monitor your posture. This covers three critical pillars: cloud infrastructure, application security, and device management across the organization. Centralized monitoring ensures misconfigurations are detected and contextualized immediately alongside your application security data. Unification prevents the visibility gaps that occur when you use disparate tools for each vector.
Accelerate the buyer's journey
Showing a live "Active" status during due diligence preempts probing questions that often stall deals. It signals operational maturity and proves that your security program is a living, breathing process. Providing a link to a live Trust Center answers potential questions instantly for security reviews. This allows security reviews to proceed smoothly and helps your sales team close deals faster.
Prioritize context over simple reporting
Continuous monitoring provides the "why" behind an alert so your team can remediate vulnerabilities instantly. Alerts without context create noise, but an effective command center correlates failures with specific risks. This shifts your culture from reactive reporting to proactive risk management that impresses enterprise buyers. Your team receives immediate context allowing them to keep your "ready" signal green and accurate.
The enterprise readiness checklist includes technical demands that modern buyers enforce to ensure deep security controls. Procurement teams in 2026 use assessments to dig into your technical execution and operational reality. You cannot bluff through these requirements because you need systems that prove controls exist today.
Continuous monitoring implements in under 24 hours and strengthens your relationship with external auditors significantly. The following answers address common concerns regarding the transition from point-in-time assessments to always-on security validation.
Q: How does continuous monitoring differ from an annual audit?
A: An audit is a point-in-time check that looks backward at a specific historical period. Continuous monitoring uses software to validate controls 24/7, catching issues immediately as they happen.
Q: Will automated evidence collection disrupt our engineering workflow?
A: No, this process actually protects your engineering workflow from constant interruptions and manual tasks. The system uses read-only APIs to collect data in the background without disturbing engineers.
Q: Can we replace our pentest with continuous monitoring?
A: No, continuous monitoring detects configuration drift while pentests find complex logic flaws in code. Regulations still require formal external pentests, so the two work best together for defense.
Q: Is a Trust Center the same as a SOC 2 report?
A: No, a SOC 2 report is a retrospective technical document meant for auditors primarily. A Trust Center is a live, customer-facing portal that displays your real-time security status.
Q: How quickly can we implement continuous monitoring?
A: Most organizations can connect their stack and establish a baseline monitoring posture in under 24 hours. Modern platforms use pre-built integrations with major cloud providers to speed up the connection.
Continuous monitoring builds a durable foundation that scales alongside your business growth and infrastructure changes. You move beyond "checkbox" compliance to achieve real-time visibility that satisfies your enterprise stakeholders. This transition adopts a mature operating model that treats security as a core business function.
Make the business case for continuous oversight
Do not view compliance as a sunk cost, but as a strategic risk requirement. By detecting misconfigurations early, you avoid the massive reputational and financial costs of breaches. Automating these processes stabilizes your security spend and prevents emergency consulting fees during audits.
Achieve faster time-to-value
Continuous monitoring keeps you audit-ready so you can unlock upmarket revenue streams significantly faster. Teams using this approach have achieved SOC 2 Type II attestation in just 6 weeks . Being audit-ready sooner means you can undergo assessment whenever your business needs require it.
Mandatory disclaimer
Mycroft supports audit readiness but does not replace an independent assessment from a qualified auditor.
Take the next step
You can see your active security posture in real-time when you build your continuous security foundation with Mycroft.